How keypad is interfaced with PIC Controller?
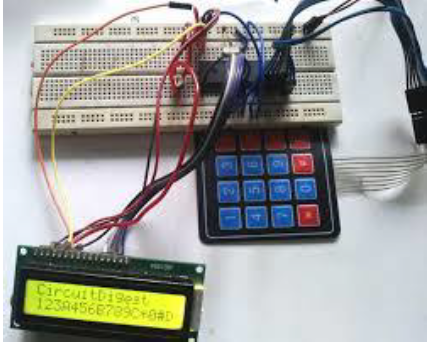
How keypad is interfaced with PIC Controller? A keypad is a group of buttons arranged in a block or pad with numbers, symbols, or alphabets. The panels that most often contain numbers and are used with computers are numeric keyboards. Keypads are found on devices that primarily require digital input.
KEYPADs INTERFACING
Matrix keyboards are very useful when designing specific systems that require user intervention. These keyboards are created by organizing the button keys into rows and columns . Scanning the keyboard for pressed keys involves several steps and there are several methods to accomplish this. The method is capable of detecting more than one keystroke at a time and encoding that information in a single 16-bit variable (int unsigned).We first discuss keypad fundamentals along with key press detection and key identification mechanism .
INTERFACING THE KEYPAD TO P1C18
When the level is low keypads are organized in a matrix of rows and columns. The CPU accesses both rows and columns through ports, therefore with two 8-bit port an 8*8 matrix of keys can be connected to a microprocessor. When a key is pressed a row and column make a contact otherwise no connection is possible. In keypad a single micro controller takes care of hardware and software interfacing of the keypad. In such systems program stored in the ROM Of micro controller scan the keys continuously, identify which one has been activated and present in to the motherboard .Programming for keypad interfacing we have two processes
➢ Key press detection
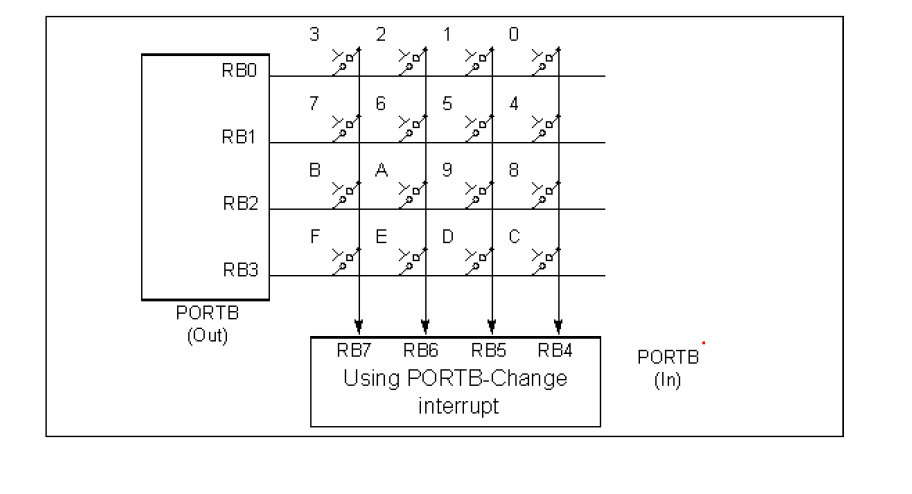
➢ Key identification There are two ways by which P1C18 can perform key press detection ➢ The interrupt method ➢ The scanning method
INTERRUPT METHOD
The device and its payment interrupt keyboard scan method accurately interpret keystrokes in single-key-press applications. Initially, the interrupts associated with each column line of the keyboard matrix are configured to execute when a key is pressed. Once the interrupt is triggered, a microcontroller polls the row lines to determine which key, if any, was pressed correctly. If exactly one keystroke is detected, the keystroke is valid. So valid key column line break is enabled while other
column line breaks are disabled. Upon receiving the next interrupt, the keyboard reverts to a row cleaning state to determine which keys are pressed. If no key is pressed, which occurs when the correctly pressed key is released, the keyboard reverts to the keystroke detection state. The method also interprets pathological keystrokes, such as a key shift, multiple keystrokes, and incorrect keystrokes.

Interrupt Method of Key Press Detection
SCANNING METHOD FOR KEY PRESS DETECTION
Another method of key press detection is by scanning .In this method to detect a pressed key a micro controller grounds all rows by providing 0 to the output latch ,then it reads the columns. If the data read from the columns are equal to 1111, no key has been pressed until a key press is detected .If one of the column bits has a zero this means the key press was occurred . After the key is pressed the microcontroller go through the identification of key pressed. Starting with the top row the micro controllers ground it by providing a low to the first row only , then it reads the column . If all the data is read , no key in that row is activated and the process is moved to the second row . It grounds the next row ,reads the next column and check for any zero .this process is continued until the row is identified . After identifying the row in which the key has been pressed , the next task is to identify in which column the key has been pressed .This is easy because the micro controller knows at any time which row and column are accessed
Some of the IC chips such as National semiconductors incorporate keyboard scanning and decoding all in one chip . Some chips uses combination of counters and logic gates to amplify some of the underlying projects .
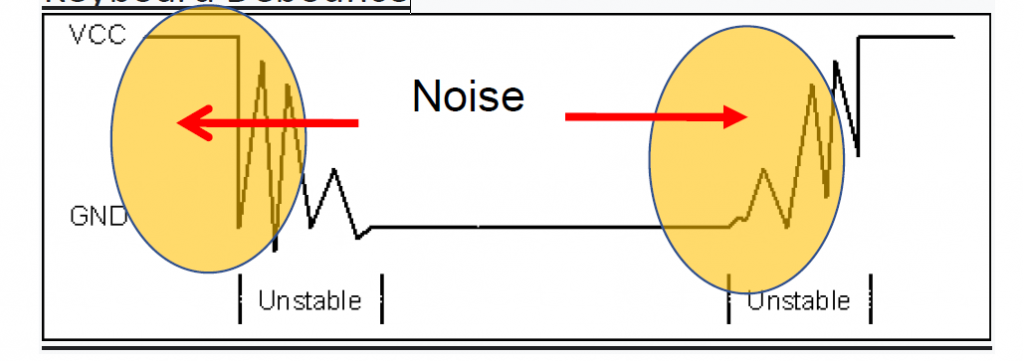
DEBOUNCING
These are spurious peaks that are generated during keystroke events. Typically, multiple spikes are generated while a switch is depressed due to mechanical contacts in the switch and cause multiple spikes, which can be detected as multiple keystroke events rather than a single
event. There you can see, there are many highs as you go from low to high. We can filter out these peaks with the help of the hardware circuit or the program routine. Hardware methods must use low-pass filters on each line, which increases the number of components in the circuit. Here we use the simplest method, We will use the timer window to read the status of the port. Enter a delay between detection and erasure By using a delay between detection and scanning we can differentiate between spikes and actual key press.
Keyboard Debounce
Also read here
Briefly write about all pins of LCD for connecting with the PIC microcontroller